Recommended administrative practice dictates that an
administrator be logged on to a privileged account (one with
administrative rights) only while doing chores that require privileges.
For ordinary work, the administrator is supposed to log off from the
privileged account and then log on again to an ordinary account. Of
course, 10 minutes later a situation usually arises requiring use of the
privileged account, making it necessary to log off from the ordinary
account and log back on to the administrator account, with the process
reversed again a few minutes later when the administrative chore is
completed.
After a few days of this,
even the most security-conscious person begins to toy with the idea of
logging on to the administrator account and staying there. In time, most
administrators succumb to the temptation and stay in the privileged
account most of the time.
This practice
makes Microsoft Windows 2000 and Windows Server 2003 systems highly
susceptible to Trojan-horse attacks. Using an administrator account
while running any browser exposes your entire network to potential
problems. Even with the very best antivirus and antispyware protection,
and a full-featured firewall, it is a bad idea to browse the Internet
with an administrative account. A Web page with Trojan-horse code can be
downloaded to the system and executed. The execution, done in the
context of administrative privileges, can cause considerable harm,
including a reformatted hard disk, the capture of critical user and
customer financial information, or the creation of a new user with
administrative access. It’s like handing the keys to your network to a
complete (and known to be malicious) stranger.
Note
For an excellent discussion
of the reasons why users should not run programs using administrator
credentials, and how to work around the problem of installing and
running programs that require administrator credentials in order to
work, see the weblog of Aaron Margosis at http://blogs.msdn.com/aaron_margosis/default.aspx.
This problem was
finally addressed in Windows 2000 with the Run As feature (enabled by
the Runas service, which is on by default). This feature, also included
in Windows Server 2003, allows you to work in a normal, nonprivileged
account and launch applications or tools while using the credentials of a
different account (most likely your administrator account) without
logging off and then logging back on again.
To use the Run As
feature, create an ordinary user account for your own use (if you don’t
have one already). Make sure that the user account has the right to log
on locally at the machine you want to use.
Note
Windows Server 2003
views all domain controllers as special cases. On a domain controller,
by default, users can’t log on locally.
Opening Programs Using Run As
To open a program or
system tool using a user account (most likely an account with
Administrator privileges) different than the one you are in, use the
following steps:
1. | Right-click the desired program, Control Panel tool, or Administrative Tools icon.
|
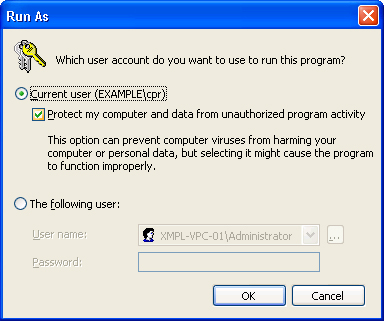
2. | Choose Run As from the shortcut menu. (See Figure 1.)
|
3. | Select The Following User, and enter the user name and password for the account you want to use.
|
4. | Click OK to open the program or tool using the specified account’s credentials.
|
You can also choose
to run the program using your current account but with restricted access
by selecting the Protect My Computer And Data From Unauthorized Program
Activity box.
Note
Some administrative tasks, such as setting system parameters, require an interactive logon and do not support Run As.
Making Shortcuts to Run As
The
idea of Run As is to encourage administrators to work outside the
administrator’s account; configuring useful shortcuts makes this more
likely to happen. Perform this task using an account without
administrative rights. Right-click an open area of the desktop, choose
New, and then choose Shortcut. Table 1 shows some examples of useful shortcuts.
Table 1. Useful Run As shortcuts
| A Shortcut to | Type |
|---|
| A command prompt with local administrative privileges. | runas /user:AdministratorAccountName@ComputerName cmd |
| A command prompt with domain administrative privileges but no profile. | runas /user:DomainAdminAccountName@Domain /noprofile cmd |
| A command prompt with domain administrative privileges. This command prompt also loads the account profile. | runas /user:DomainAdminAccountName@Domain cmd |
| Active Directory Users and Computers with domain administrative credentials. | runas /user:DomainAdminAccountName@Domain “mmc %windir%\system32\dsa.msc” |
| Performance Monitor with enterprise administrative credentials. | runas/user:EnterpriseAdminAccountName@Domain “mmc %windir%\system32\perfmon.msc” |
| Command prompt to administer server in another forest. | Runas /netonly/user:Domain\AdministratorAccountName cmd |
Keep a few of the
most frequently used shortcuts on your desktop and you’ll find it easier
to stay in your less-privileged account most of the time.
Using Runas for Printers or Control Panel
Some
applications, such as the Printers folder and Control Panel, are
launched from the shell at the time of logon, so if you’re logged on as
an ordinary user, the Control Panel functions stay in that context
(although you can open individual tools with a different account using
the runas command as shown in Table 1).
To stop the shell and
start it again as an administrator so that you can use functions such as
the Printers folder, follow these steps:
1. | Right-click the taskbar, and choose Task Manager from the shortcut menu.
|
2. | Click
the Processes tab. Select Explorer.exe, and click End Process. A
warning message appears. Click Yes. The entire desktop, except for
Windows Task Manager and any active applications, disappears.
|
3. | Select the Applications tab in Windows Task Manager, and then click New Task.
|
4. | In the Create New Task box, type runas /user:<domain\username> explorer.exe. As before, username is the account with administrative privileges. If you’re logged on locally, use the command runas /user:<machinename\username> explorer.exe.
|
5. | Enter
the password for the user name. The desktop, along with the taskbar,
returns. This desktop is in the security context of the user name you
specified in the command.
|
To return to the ordinary user’s desktop, use Task Manager again to shut down Explorer.exe. Then start a new instance by typing explorer.exe (without runas, so that Internet Explorer is restarted in the original security context) in the Create New Task dialog box.
Important
Don’t close Task
Manager while you’re working in the desktop’s administrative
context—just minimize it to the taskbar. Closing Task Manager can have
unpredictable results.
Note
You can start a
separate copy of Windows Explorer using the /separate switch. Combine
this with runas to open Explorer in a different user context. Or, if
you’re on an x64 machine and want to run a copy of 32-bit Explorer, use
it to run the 32-bit version of Explorer.exe that is in the
%windir%\SysWOW64 directory.